Utilizing a covert technique known as , hidden text salting , to bypass detection systems, Cisco Talos has discovered a growing abuse of , Cascading Style Sheet , ( CSS) properties in email-based cyberattacks.
This practice, which was tracked between March 2024 and July 2025, involves inserting useless or malicious fragments into texts while making the consumers ‘ eyes blind to the contents.
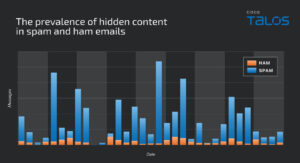
Hidden text drying has been found in spear , scam campaigns, and spam campaigns, which occurs much more often than legitimate messages, which poses challenges for both AI-driven and simple defenses.
CSS Abuse to escape recognition
Hidden text drying works by combining unidentified” salt” into email components like the , preheader, folder, parts, and figure, either random figures, multilingual words, or HTML comments. Thor documented a number of abusive behaviors:
- Text property manipulation: Using
font-size: 0, matching text color to background, or embedding zero-width spaces (ZWSP) and zero-width non-joiners (ZWNJ) between brand names such as “Norton LifeLock” to defeat keyword-based detection. - Visibility/display alteration: Setting
opacity: 0,visibility: hidden, ordisplay: noneto hide malicious text blocks inserted between legitimate content. - Clipping and sizing exploitation: Forcing container widths to zero or clipping oversized salt into invisible shapes with
overflow: hidden.
Talos discovered attackers embedding obscure words to interfere with the language protection mechanisms in programs like Microsoft Exchange Online Protection ( EOP), which cause phishing emails to appear in multilingual English-only emails.
In one case, French words hidden via display: none Confused spam filters, resulting in increased delivery success rates.
Relationships are also the main source of infection. HTML files were padding with useless Base64 comments to hinder URL processing, or with invisible European paragraphs meant to hinder dynamic research.
Cisco Secure ETD customers were targeted by lance phishing messages that displayed legit logos like those from Microsoft SharePoint and used flimsy HTML tags and covert malicious scripts.

Advanced adversaries use CSS salt to affect Large Language Model ( LLM)-driven detection pipelines.
Assailants have altered AI-derived , intent , and , sentiment  scores from” Request Action” to benign values, such as” Schedule Meeting,” allowing malicious prompts to slip through security layers undetected by adding invisible, random phrases.
Internet security reduction techniques
Talos advises using proactive and quick guarding, as well as HTML sanitization, to immediately ignore concealed content, as well as a recommendation for ingestion to strip unseen salt before processing.
To ensure that legitimate responsive designs are not erroneously flagged while destructive drying is removed, recognition models may grow beyond keyword scanning to include , analysis of physical characteristics , and cognitive detection.

This growing CSS misuse highlights the need for constant adaptation of internet security strategies, with Cisco Secure Email Threat Defense incorporating NLP, deep studying, and ML to keep resilience.
Security teams must constantly look for hidden text patterns across all invite components to combat this covert and becoming extremely potent threat vector as adversaries continue to refine unknown injection techniques.
Consider this tale Interesting! To Get More Instant Updates, Follow Us on Google News, Linked In, and X#p.